Diving into the mysterious depths of the internet can be an intriguing endeavor. For those seeking access to information and experiences concealed from the public eye, onion links serve as a passage. These encrypted connections lead to the invisible web, a realm where anonymity reigns supreme and unconventional content flourishes.
Navigating this digital underworld requires knowledge and a healthy dose of awareness. But for the intrepid, the rewards can be eye-opening.
Delving into Deep Websites with Onion Links
The dark web, a shadowy realm accessible only through specialized software and anonymous networks, contains a multitude of hidden websites. These deep sites, often referred to as "onion" sites due to their ".onion" domain extensions, provide access to a variety of content, from classified information to illicit marketplaces. To embark into this clandestine world, users require a specialized browser like Tor, which scrambles their internet traffic and directs it through a network of volunteer servers, effectively hiding their location and identity.
- Connecting to deep websites with onion links involves utilizing these browsers and navigating to the specific ".onion" address. Once connected, users can browse the content hosted on these sites, which often centers on topics that are taboo in mainstream online environments.
- However, navigating the deep web comes with inherent risks. Users should exercise extreme caution when accessing onion sites, as they may be exposed to malicious content, scams, or even legal repercussions. It is crucial to implement strong security measures and adhere to responsible browsing habits to mitigate these risks.
Deciphering the Mystery of Onion Links
Onion links have long been a intriguing enigma in the world of online anonymity. These layered links, often used to access hidden networks and websites on the invisible internet, present a unique problem for researchers and authorities.
Typically, onion links consist of strings of random symbols, which are then encoded multiple times to create a private connection. This multi-layered approach makes it highly difficult to follow the origin or destination of traffic flowing through onion links, thereby providing anonymity for users.
- However, researchers are constantly developing new methods to understand the mystery of onion links.
- For instance, some analysts are concentrating on identifying patterns in the format of onion links, hoping to expose vulnerabilities or clues about their function.
Meanwhile, the ongoing battle between those who seek to exploit onion links for malicious purposes and those who strive to combat their negative impacts will likely continue a essential aspect of the evolving cyber realm.
Navigating the Labyrinth: A Guide to Onion Links
Onion links pose a unique opportunity in the realm of online research. These complex connections, often implemented within the dark web, require a dedicated approach to accessing their hidden depths. Consider embark on a expedition to decode the intricacies of onion links, empowering you with the knowledge to effectively navigate this complex web.
- Grasping the Basics of Onion Links
- Interpreting the Architecture
- Navigating the Underworld
- Protection Measures for Onion Utilization
Beyond in Surface: Unveiling Onion Link Secrets
Dive deep within the intriguing world of onion links. These cryptic connections contain a wealth of information, waiting to be discovered. From understanding their structure to interpreting their purpose, this journey promises fascination.
- Uncover the complex nature of onion links.
- Explore the tools and techniques for analyzing these connections.
- Journey on a quest to expose the secrets hidden within.
Unveiling the Secret Web: Onion Links
Onion links, also known as .onion onionlinks addresses, open access to the hidden web, a realm where anonymity reigns supreme. This clandestine network, often shrouded in mystery and intrigue, attracts users with its promise of privacy and freedom from censorship. Within this digital underworld, individuals can engage anonymously, sharing information and ideas that may be restricted on the surface web. However, the very same anonymity that safeguards users also presents a perilous landscape. Cybercriminals, malware authors, and other nefarious actors manipulate the hidden web for illicit activities, ranging from drug trafficking and arms dealing to identity theft and financial fraud.
Navigating this complex ecosystem requires caution. Users must be aware of the risks inherent in accessing .onion sites, taking steps to protect their security. While the hidden web offers a platform for freedom and expression, it also shelters a darker side that demands utmost attention.
 Haley Joel Osment Then & Now!
Haley Joel Osment Then & Now!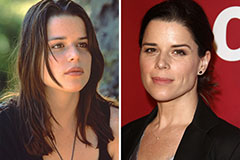 Neve Campbell Then & Now!
Neve Campbell Then & Now! Ariana Richards Then & Now!
Ariana Richards Then & Now! Hallie Eisenberg Then & Now!
Hallie Eisenberg Then & Now! Suri Cruise Then & Now!
Suri Cruise Then & Now!